upload-labs靶场1-18关解法总结
目录
PASS-1
PASS-2
PASS-3
PASS-4
PASS-5
PASS-6
PASS-7
PASS-8
PASS-9
PASS-10
PASS-11
PASS-12
PASS-13
PASS-14
PASS-15
PASS-16
PASS-17
PASS-18
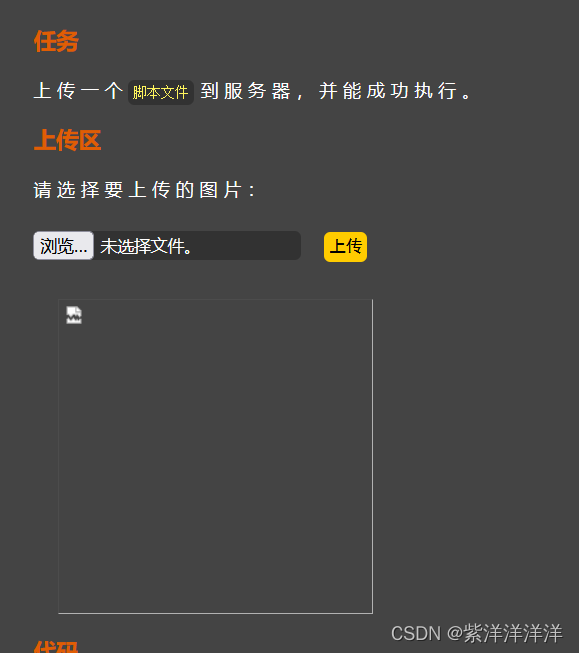
PASS-1
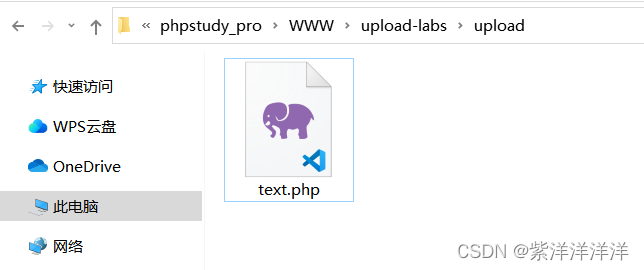
我们试着上传一个php文件,文件内容为
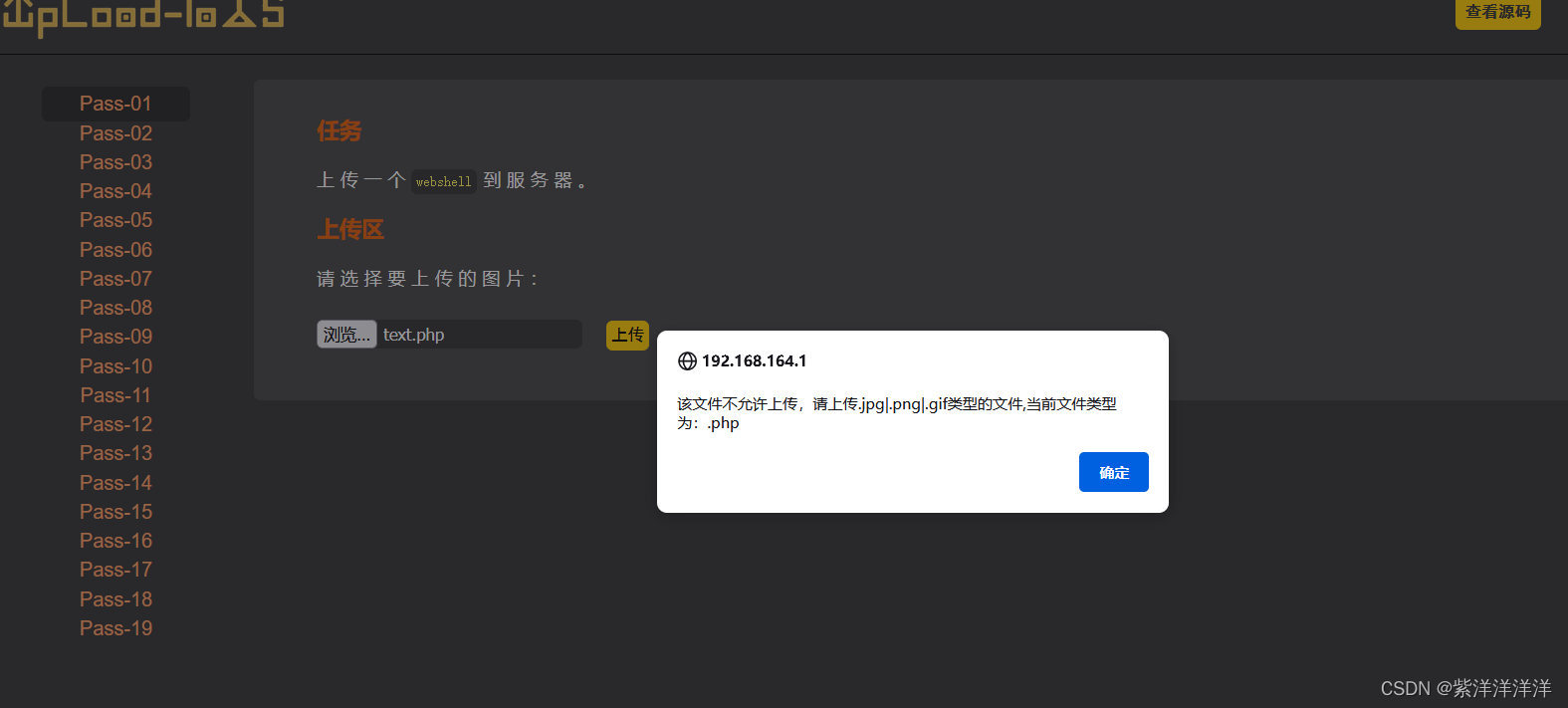
弹窗显示不允许上传,说明运用了前端验证
我们可以利用brupsuite工具进行抓包,在burp中将文件后缀名改为我们想更改的格式,再进行上传,这样我们可以绕过前端检测
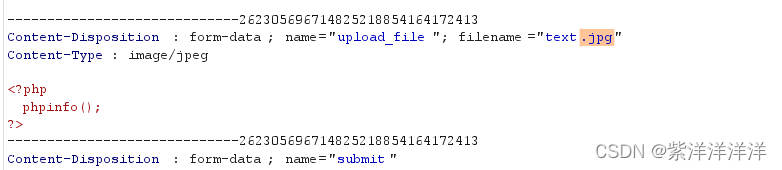
将JPG格式改为PHP格式后点Forward进行放包
上传成功,文件在upload里
PASS-2
和第一关一样,先上传看看回显事什么样的
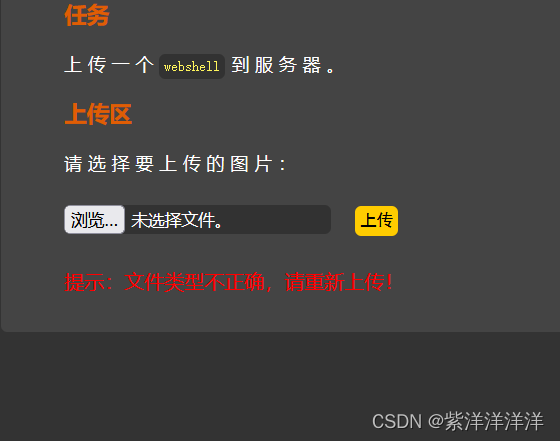
错误回显方式不是弹窗,而是页面直接提示,所以不是前端验证。查看源码
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists($UPLOAD_ADDR)) {if (($_FILES['upload_file']['type'] == 'image/jpeg') || ($_FILES['upload_file']['type'] == 'image/png') || ($_FILES['upload_file']['type'] == 'image/gif')) {if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {$img_path = $UPLOAD_ADDR . $_FILES['upload_file']['name'];$is_upload = true;}} else {$msg = '文件类型不正确,请重新上传!';}} else {$msg = $UPLOAD_ADDR.'文件夹不存在,请手工创建!';}
}
上传文件的途中是验证了content-type,并且固定了可以上传的文件类型,解决方法还是用burpsuite修改content-type信息
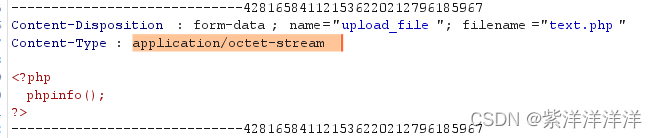
修改为 image/jpeg 后上传即可
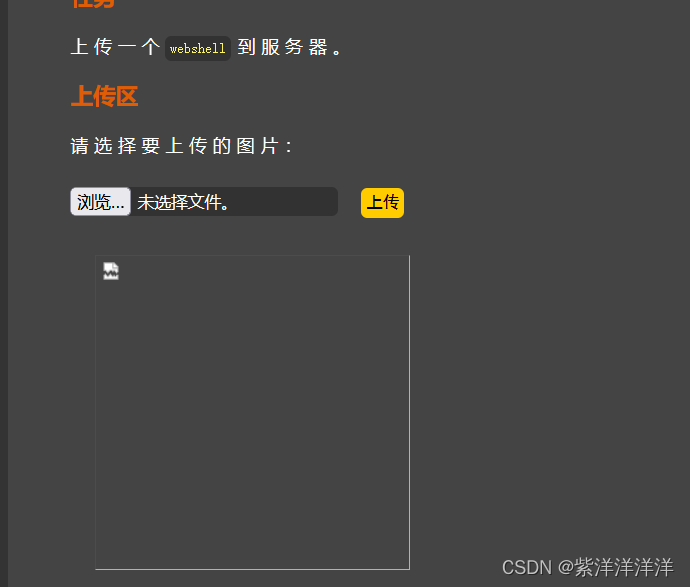
上传成功
PASS-3
第三关提示上传一个脚本文件,我们查看源码
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists($UPLOAD_ADDR)) {$deny_ext = array('.asp','.aspx','.php','.jsp');$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //收尾去空if(!in_array($file_ext, $deny_ext)) {if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR. '/' . $_FILES['upload_file']['name'])) {$img_path = $UPLOAD_ADDR .'/'. $_FILES['upload_file']['name'];$is_upload = true;}} else {$msg = '不允许上传.asp,.aspx,.php,.jsp后缀文件!';}} else {$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';}
}
'.asp','.aspx','.php','.jsp'后缀的文件都不允许上传,并且会检查大小写、删除点和空格
现在想上传一个'.php'后缀的文件,可以使用一些php文件的其他拓展名
.php .phtml .phps .php5 .pht
修改扩展名后继续上传
上传成功
PASS-4
源码分析
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists($UPLOAD_ADDR)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2","php1",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2","pHp1",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //收尾去空if (!in_array($file_ext, $deny_ext)) {if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {$img_path = $UPLOAD_ADDR . $_FILES['upload_file']['name'];$is_upload = true;}} else {$msg = '此文件不允许上传!';}} else {$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';}
}将扩展名都禁用了
这关可以选择 '.htaccess' 文件进行绕过
'.htaccess'文件相当于一种部分配置文件,好比局部变量一样,只在当前目录生效。比如你设置解析'.txt'解析为'.php',那么'.htaccess'文件在的子目录中就会执行,而上一级目录不执行。
创建'.htaccess'文件,然后在其中写入代码,使得文件在解析时将'.jpg'文件解析为'.php'文件
SetHandler application/x-httpd-php 在上传时我们只需要将文件后缀名改为'.jpg',访问时会自动被执行为'.php'文件。
PASS-5
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists(UPLOAD_PATH)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //首尾去空if (!in_array($file_ext, $deny_ext)) {$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = UPLOAD_PATH.'/'.$file_name;if (move_uploaded_file($temp_file, $img_path)) {$is_upload = true;} else {$msg = '上传出错!';}} else {$msg = '此文件类型不允许上传!';}} else {$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';}
}
本关使用点空格点绕过即可
把文件名修改为“text.php. . ”
PASS-6
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists($UPLOAD_ADDR)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //首尾去空if (!in_array($file_ext, $deny_ext)) {if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {$img_path = $UPLOAD_ADDR . '/' . $file_name;$is_upload = true;}} else {$msg = '此文件不允许上传';}} else {$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';}
}
第五关根据源码分析可知没有了大小写限制,可以将文件后缀名改为 '.Php' 上传
PASS-7
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists($UPLOAD_ADDR)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATAif (!in_array($file_ext, $deny_ext)) {if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {$img_path = $UPLOAD_ADDR . '/' . $file_name;$is_upload = true;}} else {$msg = '此文件不允许上传';}} else {$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';}
}第六关根据源码分析可知没有了删除空格的代码,可以在文件后缀名末尾添加空格,如'test.php'改写为'test.php ',windos在存储时会自动去处空格,但在检测时可以绕过黑名单限制。
PASS-8
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists($UPLOAD_ADDR)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");$file_name = trim($_FILES['upload_file']['name']);$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //首尾去空if (!in_array($file_ext, $deny_ext)) {if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {$img_path = $UPLOAD_ADDR . '/' . $file_name;$is_upload = true;}} else {$msg = '此文件不允许上传';}} else {$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';}
}
第七关没有删除文件末尾点的代码,所以可以在文件后缀名后加点,如'test.php'改写为'test.php.',Windows存储时也会自动去除后缀名末尾的点,但检测时可绕过黑名单
PASS-9
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists($UPLOAD_ADDR)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = trim($file_ext); //首尾去空if (!in_array($file_ext, $deny_ext)) {if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {$img_path = $UPLOAD_ADDR . '/' . $file_name;$is_upload = true;}} else {$msg = '此文件不允许上传';}} else {$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';}
}第八关缺少限制类型::$DATA类型
当php在windows环境的时候,如果文件名+ “::$DATA" 会 把 "::$DATA" 之后的数据当成文件流处理,不会检测后缀名.且保持"::$DATA"之前的文件名
‘test.php’改写为'test.php::$DATA'
PASS-10
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists($UPLOAD_ADDR)) {$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");$file_name = trim($_FILES['upload_file']['name']);$file_name = deldot($file_name);//删除文件名末尾的点$file_ext = strrchr($file_name, '.');$file_ext = strtolower($file_ext); //转换为小写$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA$file_ext = trim($file_ext); //首尾去空if (!in_array($file_ext, $deny_ext)) {if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {$img_path = $UPLOAD_ADDR . '/' . $file_name;$is_upload = true;}} else {$msg = '此文件不允许上传';}} else {$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';}
}利用检测机制将‘test.php’改写为'test.php. .'
PASS-11
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {if (file_exists($UPLOAD_ADDR)) {$deny_ext = array("php","php5","php4","php3","php2","html","htm","phtml","jsp","jspa","jspx","jsw","jsv","jspf","jtml","asp","aspx","asa","asax","ascx","ashx","asmx","cer","swf","htaccess");$file_name = trim($_FILES['upload_file']['name']);$file_name = str_ireplace($deny_ext,"", $file_name);if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $file_name)) {$img_path = $UPLOAD_ADDR . '/' .$file_name;$is_upload = true;}} else {$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';}
}与黑名单相同的后缀名会被替换为空,我们可以进行双写绕过
‘test.php’改写为'test.pphphp'
PASS-12
$is_upload = false;
$msg = null;
if(isset($_POST['submit'])){$ext_arr = array('jpg','png','gif');$file_ext = substr($_FILES['upload_file']['name'],strrpos($_FILES['upload_file']['name'],".")+1);if(in_array($file_ext,$ext_arr)){$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = $_GET['save_path']."/".rand(10, 99).date("YmdHis").".".$file_ext;if(move_uploaded_file($temp_file,$img_path)){$is_upload = true;} else {$msg = '上传出错!';}} else{$msg = "只允许上传.jpg|.png|.gif类型文件!";}
}
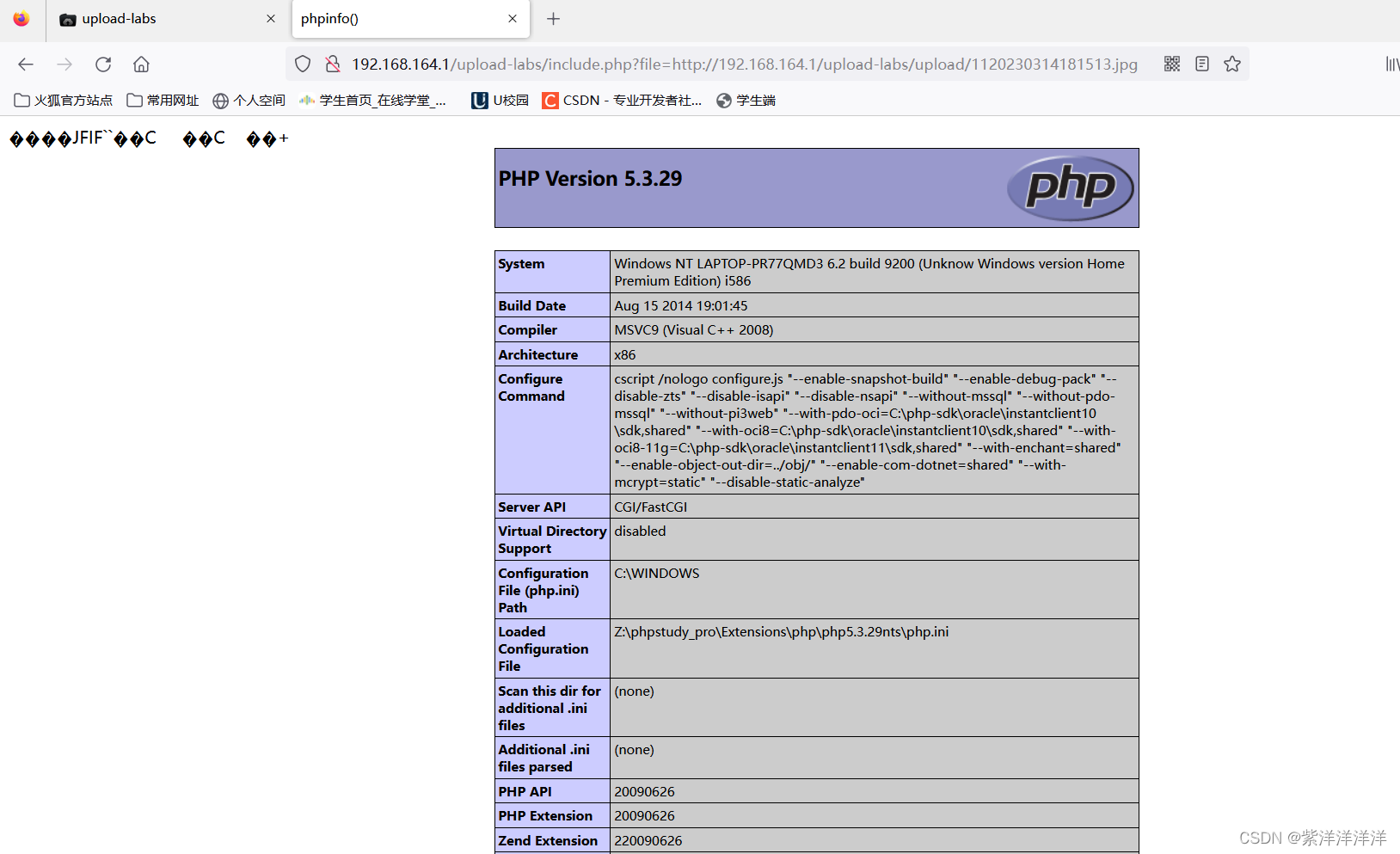
Pass-12首先提取了文件后缀名,只允许上传图片文件,但上传路径是可控的,所以我们可以使用%00截断漏洞将上传路径改为文件名。当使用了截断漏洞时,传入的文件名为shell.php%00shell.jpg,检测时发现后缀为.jpg,所以没有过滤;保存时由于使用了%00截断,%00后面的字符串不生效,所以最后保存的文件名是shell.php
00截断的使用条件:
(1)php版本要小于5.3.4。
(2)文件路径可控。
(3)magic_quotes_gpc需要为OFF状态。(在php.ini中)
PASS-13
$is_upload = false;
$msg = null;
if(isset($_POST['submit'])){$ext_arr = array('jpg','png','gif');$file_ext = substr($_FILES['upload_file']['name'],strrpos($_FILES['upload_file']['name'],".")+1);if(in_array($file_ext,$ext_arr)){$temp_file = $_FILES['upload_file']['tmp_name'];$img_path = $_POST['save_path']."/".rand(10, 99).date("YmdHis").".".$file_ext;if(move_uploaded_file($temp_file,$img_path)){$is_upload = true;} else {$msg = "上传失败";}} else {$msg = "只允许上传.jpg|.png|.gif类型文件!";}
}
Pass考察基于POST方法的截断上传攻击。POST方法较为特殊,直接在明文中添加%00不会被服务器解码,我们需要修改HTTP包中上传路径对应的十六进制值(改为00)进行截断攻击,其原理与Pass-12相同
burp抓包时点击Hex选项卡,找到“text.jpg”这段字符串对应的十六进制数据,将61(a的十六进制ASCII码)前面的数值(对应空格)改为00后放包上传即可
PASS-14
function getReailFileType($filename){$file = fopen($filename, "rb");$bin = fread($file, 2); //只读2字节fclose($file);$strInfo = @unpack("C2chars", $bin); $typeCode = intval($strInfo['chars1'].$strInfo['chars2']); $fileType = ''; switch($typeCode){ case 255216: $fileType = 'jpg';break;case 13780: $fileType = 'png';break; case 7173: $fileType = 'gif';break;default: $fileType = 'unknown';} return $fileType;
}$is_upload = false;
$msg = null;
if(isset($_POST['submit'])){$temp_file = $_FILES['upload_file']['tmp_name'];$file_type = getReailFileType($temp_file);if($file_type == 'unknown'){$msg = "文件未知,上传失败!";}else{$img_path = UPLOAD_PATH."/".rand(10, 99).date("YmdHis").".".$file_type;if(move_uploaded_file($temp_file,$img_path)){$is_upload = true;} else {$msg = "上传出错!";}}
}这一关会读取判断上传文件的前两个字节,判断上传文件类型,并且后端会根据判断得到的文件类型重命名上传文件
使用图片马和文件包含绕过
创建图片马
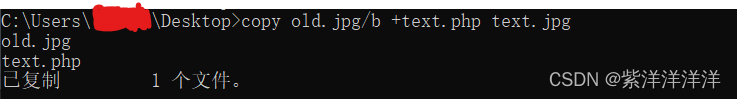 上传图片马文件后访问include.php,将参数设置为图片木马的URL
上传图片马文件后访问include.php,将参数设置为图片木马的URL
PASS-15
function isImage($filename){$types = '.jpeg|.png|.gif';if(file_exists($filename)){$info = getimagesize($filename);$ext = image_type_to_extension($info[2]);if(stripos($types,$ext)>=0){return $ext;}else{return false;}}else{return false;}
}$is_upload = false;
$msg = null;
if(isset($_POST['submit'])){$temp_file = $_FILES['upload_file']['tmp_name'];$res = isImage($temp_file);if(!$res){$msg = "文件未知,上传失败!";}else{$img_path = UPLOAD_PATH."/".rand(10, 99).date("YmdHis").$res;if(move_uploaded_file($temp_file,$img_path)){$is_upload = true;} else {$msg = "上传出错!";}}
}
getimagesize()检查是否为图片文件,所以还是可以用第十四关的图片马绕过,并使用文件包含漏洞解析图片马
PASS-16
function isImage($filename){//需要开启php_exif模块$image_type = exif_imagetype($filename);switch ($image_type) {case IMAGETYPE_GIF:return "gif";break;case IMAGETYPE_JPEG:return "jpg";break;case IMAGETYPE_PNG:return "png";break; default:return false;break;}
}$is_upload = false;
$msg = null;
if(isset($_POST['submit'])){$temp_file = $_FILES['upload_file']['tmp_name'];$res = isImage($temp_file);if(!$res){$msg = "文件未知,上传失败!";}else{$img_path = UPLOAD_PATH."/".rand(10, 99).date("YmdHis").".".$res;if(move_uploaded_file($temp_file,$img_path)){$is_upload = true;} else {$msg = "上传出错!";}}
}
exif_imagetype()读取一个图像的第一个字节并检查其后缀名.
只要图片木马能在本地用照片浏览器正常地打开,就能用文件解析漏洞绕过
方法同PASS-14
PASS-17
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])){// 获得上传文件的基本信息,文件名,类型,大小,临时文件路径$filename = $_FILES['upload_file']['name'];$filetype = $_FILES['upload_file']['type'];$tmpname = $_FILES['upload_file']['tmp_name'];$target_path=UPLOAD_PATH.'/'.basename($filename);// 获得上传文件的扩展名$fileext= substr(strrchr($filename,"."),1);//判断文件后缀与类型,合法才进行上传操作if(($fileext == "jpg") && ($filetype=="image/jpeg")){if(move_uploaded_file($tmpname,$target_path)){//使用上传的图片生成新的图片$im = imagecreatefromjpeg($target_path);if($im == false){$msg = "该文件不是jpg格式的图片!";@unlink($target_path);}else{//给新图片指定文件名srand(time());$newfilename = strval(rand()).".jpg";//显示二次渲染后的图片(使用用户上传图片生成的新图片)$img_path = UPLOAD_PATH.'/'.$newfilename;imagejpeg($im,$img_path);@unlink($target_path);$is_upload = true;}} else {$msg = "上传出错!";}}else if(($fileext == "png") && ($filetype=="image/png")){if(move_uploaded_file($tmpname,$target_path)){//使用上传的图片生成新的图片$im = imagecreatefrompng($target_path);if($im == false){$msg = "该文件不是png格式的图片!";@unlink($target_path);}else{//给新图片指定文件名srand(time());$newfilename = strval(rand()).".png";//显示二次渲染后的图片(使用用户上传图片生成的新图片)$img_path = UPLOAD_PATH.'/'.$newfilename;imagepng($im,$img_path);@unlink($target_path);$is_upload = true; }} else {$msg = "上传出错!";}}else if(($fileext == "gif") && ($filetype=="image/gif")){if(move_uploaded_file($tmpname,$target_path)){//使用上传的图片生成新的图片$im = imagecreatefromgif($target_path);if($im == false){$msg = "该文件不是gif格式的图片!";@unlink($target_path);}else{//给新图片指定文件名srand(time());$newfilename = strval(rand()).".gif";//显示二次渲染后的图片(使用用户上传图片生成的新图片)$img_path = UPLOAD_PATH.'/'.$newfilename;imagegif($im,$img_path);@unlink($target_path);$is_upload = true;}} else {$msg = "上传出错!";}}else{$msg = "只允许上传后缀为.jpg|.png|.gif的图片文件!";}
}本关进行了二次渲染,需要找到渲染后的图片里面没有发生变化的Hex地方,添加一句话,通过文件包含漏洞执行一句话
PASS-18
$is_upload = false;
$msg = null;if(isset($_POST['submit'])){$ext_arr = array('jpg','png','gif');$file_name = $_FILES['upload_file']['name'];$temp_file = $_FILES['upload_file']['tmp_name'];$file_ext = substr($file_name,strrpos($file_name,".")+1);$upload_file = UPLOAD_PATH . '/' . $file_name;if(move_uploaded_file($temp_file, $upload_file)){if(in_array($file_ext,$ext_arr)){$img_path = UPLOAD_PATH . '/'. rand(10, 99).date("YmdHis").".".$file_ext;rename($upload_file, $img_path);$is_upload = true;}else{$msg = "只允许上传.jpg|.png|.gif类型文件!";unlink($upload_file);}}else{$msg = '上传出错!';}
}
服务器先是将上传的文件保存下来,然后将文件的后缀名同白名单对比,如果是jpg、png、gif中的一种,就将文件进行重命名。如果不符合的话,unlink()函数就会删除该文件。
如果我们能在上传的一句话被删除之前访问就成了。这个也就叫做条件竞争上传绕过。
我们可以利用burp多线程发包,然后不断在浏览器访问我们的webshell,会有一瞬间的访问成功,一旦访问到该文件就会在当前目录下生成一句话木马
上一篇:如何设计一个底层埋点?
下一篇:逻辑回归全面解析
